CrowdStrike Falcon Intelligence Operation
The web format of this guide reflects the most current release. Guides for older iterations are available in PDF format.
Integration Details
ThreatQuotient provides the following details for this integration:
| Current Integration Version | 1.0.0 |
| Compatible with ThreatQ Versions | >= 5.20.0 |
| Support Tier | ThreatQ Supported |
Introduction
The CrowdStrike Falcon Intelligence operation queries the CrowdStrike Falcon Intelligence API to retrieve further information about submitted indicators.
The operation provides the following action:
- Query - queries the CrowdStrike Falcon Intelligence API for further information on the submitted indicator.
The operation is compatible with indicator type system objects.
Prerequisites
The following is required in order to run the operation:
- CrowdStrike Client ID and Client Secret
- Properly scoped CrowdStrike API Client
- MITRE ATT&CK Feeds (optional)
CrowdStrike API Client
To use the CrowdStrike Falcon Intelligence resources, you must create a properly scoped API Client within CrowdStrike's Falcon platform. API Clients can be created and configured via the API Clients and Keys page under Support. An API Client must be created for this operation and given the following API Read Scopes by clicking the Add new API Client button:
- Actors (Falcon X)
- Indicators (Falcon X)
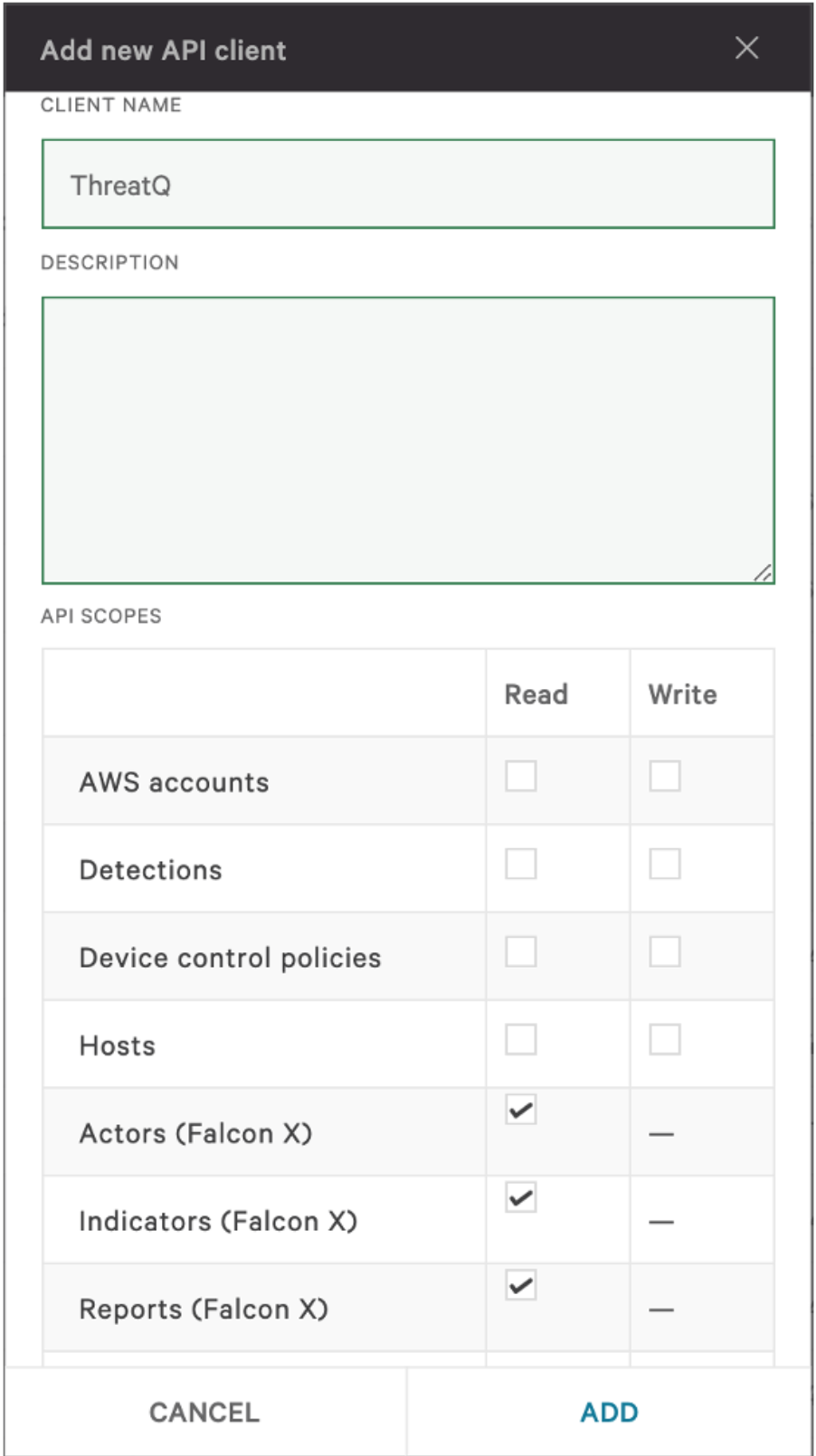
It is typically a good idea to give the API Client an identifiable name in case of future editing.
MITRE ATT&CK Feeds
To automatically ingest Attack Patterns, please make sure you have installed and run the following feeds successfully before using this operation:
- MITRE Enterprise ATT&CK
- MITRE Mobile ATT&CK
- MITRE PRE-ATT&CK
Installation
Perform the following steps to install the integration:
The same steps can be used to upgrade the integration to a new version.
- Log into https://marketplace.threatq.com/.
- Locate and download the integration whl file.
- Navigate to the integrations management page on your ThreatQ instance.
- Click on the Add New Integration button.
- Upload the whl file using one of the following methods:
- Drag and drop the file into the dialog box
- Select Click to Browse to locate the file on your local machine
ThreatQ will inform you if the operation already exists on the platform and will require user confirmation before proceeding. ThreatQ will also inform you if the new version of the operation contains changes to the user configuration. The new user configurations will overwrite the existing ones for the operation and will require user confirmation before proceeding.
The operation is now installed and will be displayed in the ThreatQ UI. You will still need to configure and then enable the operation.
Configuration
ThreatQuotient does not issue API keys for third-party vendors. Contact the specific vendor to obtain API keys and other integration-related credentials.
To configure the integration:
- Navigate to your integrations management page in ThreatQ.
- Select the Operation option from the Type dropdown (optional).
- Click on the integration entry to open its details page.
- Enter the following parameters under the Configuration tab:
Parameter Description API Hostname The API host to communicate with CrowdStrike. CrowdStrike Client ID The CrowdStrike Client ID used to authenticate. CrowdStrike Client Secret The CrowdStrike Client Secret used to authenticate. - Review any additional settings, make any changes if needed, and click on Save.
- Click on the toggle switch, located above the Additional Information section, to enable it.
Actions
The operation provides the following action:
| Action | Description | Object Type | Object Subtype |
|---|---|---|---|
| Query | Queries Crowdstrike Falcon Intelligence API for an indicator | Indicator | All |
Query
The Query action queries Crowdstrike Falcon Intelligence API for an indicator.
POST https://{host}/intel/combined/indicators/v1
Sample Request Body:
{
"filter": "indicator: 'cb0fa82c79b7eed6ba356991c4c89161403162ef56d4e76c528bca857b08cb7a'",
"sort": "last_updated|desc",
"limit": 1
}Sample Response:
{
"meta": {
"query_time": 0.053664582,
"pagination": {
"offset": 0,
"limit": 1,
"total": 1
},
"powered_by": "msa-api",
"trace_id": "e6e8a29a-dacd-4aca-bb69-24e8251dd843"
},
"resources": [
{
"id": "hash_sha256_cb0fa82c79b7eed6ba356991c4c89161403162ef56d4e76c528bca857b08cb7a",
"indicator": "cb0fa82c79b7eed6ba356991c4c89161403162ef56d4e76c528bca857b08cb7a",
"type": "hash_sha256",
"deleted": false,
"published_date": 1708907561,
"last_updated": 1709724487,
"reports": [
"CSA-18538"
],
"actors": [
"FANCYBEAR"
],
"malware_families": [
"ContiRansomware"
],
"kill_chains": [
"ActionOnObjectives"
],
"ip_address_types": [
"TorProxy"
],
"domain_types": [
"ActorControlled"
],
"malicious_confidence": "high",
"_marker": "1709724487150f1363aeae1c25de63a7a8b2814fb9",
"labels": [
{
"name": "MitreATTCK/Impact/QueryRegistry",
"created_on": 1708907563,
"last_valid_on": 1708907563
},
{
"name": "ThreatType/Criminal",
"created_on": 1595592139,
"last_valid_on": 1693409035
}
],
"relations": [
{
"id": "hash_sha1_d17c1a5550fab6ce451df922781fe8534dcd9167",
"indicator": "d17c1a5550fab6ce451df922781fe8534dcd9167",
"type": "hash_sha1",
"created_date": 1708907561,
"last_valid_date": 1708907561
}
],
"targets": [
"Finance"
],
"threat_types": [
"Criminal",
"Ransomware"
],
"vulnerabilities": [
"CVE-2020-1234"
]
}
],
"errors": []
}ThreatQuotient provides the following default mapping for this action:
| Feed Data Path | ThreatQ Entity | ThreatQ Object Type or Attribute Key | Published Date | Examples | Notes |
|---|---|---|---|---|---|
| .resources[].actors | Adversary.Name | N/A | N/A | FANCY BEAR | Actor names are split into two words in order to overlap with records from the CrowdStrike Actors Feed on ingestion |
| .resources[].malware_ families |
Malware.Value | N/A | N/A | ContiRansomware | N/A |
| .resources[].kill_chains | Indicator.Attribute | Kill Chain Phase | N/A | CommandAndControl | N/A |
| .resources[].ip_ address_types |
Indicator.Attribute | IP Address Type | N/A | TorProxy | N/A |
| .resources[].domain_ types |
Indicator.Attribute | Domain Type | N/A | ActorControlled | N/A |
| .resources[]. malicious_ confidence |
Indicator.Attribute | Confidence | N/A | High | Value title cased |
| .resources[]. labels[].name |
AttackPattern.Value | N/A | N/A | T1012 - Query Registry | If an Indicator has any MitreATTCK labels (e.g. MitreATTCK/Discovery/QueryRegistry) and if the attack pattern name in the label (e.g. QueryRegistry) matches the attack pattern name of MITRE ATT&CK Attack Patterns that already exist in the ThreatQ system (e.g. T1012 - Query Registry), the associated attack patterns are related to the Indicator |
| .resources[].relations[] .indicator |
Related Indicator.Value | See .resources[].relations[].type | N/A | d17c1a5550fab6ce451df922781fe8534dcd9167 |
N/A |
| .resources[]. relations[].type |
Related Indicator.Type | See Indicator Type Mapping table below | N/A | SHA-1 | N/A |
| .resources[].targets | Indicator.Attribute | Target Industry | N/A | Finance | N/A |
| .resources[]. threat_types |
Indicator.Attribute | Threat Type | N/A | Criminal | Single Camel-case values will be broken up into multiple words, eg. CredentialHarvesting->Credential Harvesting |
| .resources[]. vulnerabilities |
Related Indicator.Value | CVE | N/A | CVE-2020-1234 | N/A |
Run Parameters
The following parameters are available when selecting to run the Action against an object:
| Parameter | Description |
|---|---|
| Create an attribute from related malware: | Show related malware as the attribute Related Malware in the operation result. |
| Create an attribute from related adversaries: | Show related adversaries as the attribute Related Adversary in the operation result. |
| Create relationships for related malware during operation run: | Create relationships for related malware during operation run |
| Create relationships for related adversaries during operation run: | Create relationships for related adversaries during operation run |
| Create relationships for related attack patterns during operation run: | Create relationships for related attack patterns during operation run |
Indicator Type Mapping
The following tables provides CrowdStrike to ThreatQ Indicator type mapping.
| CrowdStrike Indicator Type | ThreatQ Indicator Type |
|---|---|
| binary_string | Binary String |
| domain | FQDN |
| email_address | Email Address |
| email_subject | Email Subject |
| file_mapping | File Mapping |
| file_name | Filename |
| file_path | File Path |
| hash_ion | Hash ION |
| hash_md5 | MD5 |
| hash_sha1 | SHA-1 |
| hash_sha256 | SHA-256 |
| ip_address | IP Address |
| ip_address_block | CIDR Block |
| mutex_name | Mutex |
| password | Password |
| registry | Registry Key |
| service_name | Service Name |
| url | URL |
| user_agent | User-agent |
| username | Username |
| x509_serial | x509 Serial |
| x509_subject | x509 Subject |
Change Log
- Version 1.0.0
- Initial release
PDF Guides
| Document | ThreatQ Version |
|---|---|
| CrowdStrike Falcon Intelligence Operation Guide v1.0.0 | 5.20.0 or Greater |