Kaspersky C&C Tracking CDF
The web format of this guide reflects the most current release. Guides for older iterations are available in PDF format.
Integration Details
ThreatQuotient provides the following details for this integration:
| Current Integration Version | 1.0.3 |
| Compatible with ThreatQ Versions | >= 4.37.0 |
| Support Tier | ThreatQ Supported |
Introduction
The Kaspersky C&C Tracking CDF ingests IP Addresses and related ASN data from the Kaspersky C&C Tracking API.
The Kaspersky C&C Tracking CDF integration for ThreatQ provides the following feed:
- Kaspersky C&C Tracking Feed - ingests IP Addresses of infrastructure connected to advanced threats and ASN data.
The integration ingests the following system objects:
- Indicators
- Indicator Attributes
Installation
This integration can be installed in the My Integration section of your ThreatQ instance. See the Adding an Integration topic for more details.
Configuration
ThreatQuotient does not issue API keys for third-party vendors. Contact the specific vendor to obtain API keys and other integration-related credentials.
To configure the integration:
- Navigate to your integrations management page in ThreatQ.
- Select the Commercial option from the Category dropdown (optional).
If you are installing the integration for the first time, it will be located under the Disabled tab.
- Click on the integration entry to open its details page.
- Enter the following parameters under the Configuration tab:
Parameter Description Account Username Your Kaspersky account username. Account Password The password associated with the username above. Kaspersky PEM File Your Kaspersky PEM file.
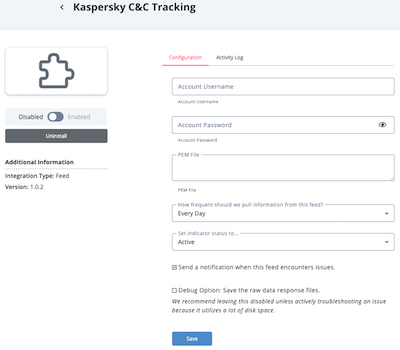
- Review any additional settings, make any changes if needed, and click on Save.
- Click on the toggle switch, located above the Additional Information section, to enable it.
ThreatQ Mapping
Kaspersky C&C Tracking Feed
The Kaspersky C&C Tracking feed ingests IP Addresses of infrastructure connected to advanced threats and ASN data.
GET https://tip.kaspersky.com/api/apt_cnc/all
Sample Response:
[
{
"ip": "54.215.129.6" ,
"first_seen": "2021-04-18" ,
"last_seen": "2021-04-18" ,
"country_code": "us" ,
"tags": [
{
"name": "CobaltStrike" ,
"source": null ,
"type": "Organic" ,
"description": "Cobalt Strike is a commercially available attack platform developed by Raphael Mudge and used by multiple threat actors."
}
] ,
"asn": 16509 ,
"asn_name": "AMAZON-02" ,
"ip_whois": {
"net_range": "54.215.0.0 - 54.215.255.255" ,
"net_name": "AMAZO-ZSFO2" ,
"descr": null ,
"created": "2013-03-19" ,
"updated": "2013-03-19" ,
"country": null ,
"city": null ,
"contact_owner_name": "Amazon.com, Inc." ,
"contact_owner_code": "AMAZO-48" ,
"contact_owner_country": "US" ,
"contact_owner_city": "Seattle" ,
"contact_owner_email": "amzn-noc-contact@amazon.com" ,
"contact_abuse_name": "Amazon EC2 Abuse" ,
"contact_abuse_country": null ,
"contact_abuse_city": null ,
"contact_abuse_email": "abuse@amazonaws.com" ,
"net_asn": "16509"
}
} ,
{
"ip": "72.45.135.213" ,
"first_seen": "2021-04-18" ,
"last_seen": "2021-04-18" ,
"country_code": "us" ,
"tags": [
{
"name": "CobaltStrike" ,
"source": null ,
"type": "Organic" ,
"description": "Cobalt Strike is a commercially available attack platform developed by Raphael Mudge and used by multiple threat actors."
}
] ,
"asn": 11351 ,
"asn_name": "TWC-11351-NORTHEAST" ,
"ip_whois": {
"net_range": "72.45.128.0 - 72.45.255.255" ,
"net_name": "RCACI" ,
"descr": null ,
"created": "2006-08-10" ,
"updated": "2007-07-18" ,
"country": null ,
"city": null ,
"contact_owner_name": "Time Warner Cable Internet LLC" ,
"contact_owner_code": "RCNY" ,
"contact_owner_country": "US" ,
"contact_owner_city": "Herndon" ,
"contact_owner_email": "abuse@rr.com" ,
"contact_abuse_name": "Abuse" ,
"contact_abuse_country": null ,
"contact_abuse_city": null ,
"contact_abuse_email": "abuse@rr.com" ,
"net_asn": null
}
}
]ThreatQuotient provides the following default mapping for this feed:
| Feed Data Path | ThreatQ Entity | ThreatQ Object Type or Attribute Key | Published Date | Examples | Notes |
|---|---|---|---|---|---|
| .return_data[].ip | Indicator.Value | IP Address | .return_data[].first_seen | 140.82.41.202 | N/A |
| return_data[].country_code | Indicator.Attribute | Country code | .return_data[].first_seen | us | N/A |
| return_data[].tags[].name | Indicator.Attribute | Tag Name | .return_data[].first_seen | Empire C2 | N/A |
| return_data[].asn | Related Indicator.Value | ASN | .return_data[].first_seen | 20473 | N/A |
| return_data[].asn_name | Indicator.Attribute | ASN Name | .return_data[].first_seen | AS-CHOOPA | N/A |
Average Feed Run
Object counts and Feed runtime are supplied as generalities only - objects returned by a provider can differ based on credential configurations and Feed runtime may vary based on system resources and load.
| Metric | Result |
|---|---|
| Run Time | 12 min |
| Indicators | 9,552 |
| Indicator Attributes | 21,942 |
Change Log
- Version 1.0.3
- Fixed a UI issue that would ignore an indicator status upon ingestion.
- Version 1.0.2
- Fixed the response property that contains the data that is ingested.
- Version 1.0.1
- Added support between IP Address Indicators and their ASN data.
- Updated integration support tier from Not Supported to ThreatQ Supported.
- Version 1.0.0
- Initial Release
PDF Guides
| Document | ThreatQ Version |
|---|---|
| Kaspersky C&C Tracking CDF Guide v1.0.3 | 4.37.0 or Greater |
| Kaspersky C&C Tracking CDF Guide v1.0.2 | 4.37.0 or Greater |
| Kaspersky C&C Tracking CDF Guide v1.0.1 | 4.37.0 or Greater |
| Kaspersky C&C Tracking CDF Guide v1.0.0 | 4.37.0 or Greater |