FS-ISAC CDF
The web format of this guide reflects the most current release. Guides for older iterations are available in PDF format.
Integration Details
ThreatQuotient provides the following details for this integration:
| Current Integration Version | 1.1.0 |
| Compatible with ThreatQ Versions | >= 5.29.0 |
| Support Tier | ThreatQ Supported |
Introduction
FS-ISAC is an intelligence sharing community for financial services organizations. FS-ISAC provides feeds to their members containing intelligence surrounding threats targeting their industry. The FS-ISAC CDF enables the automatic ingestion of FS-ISAC feeds into ThreatQ. This integration acts as a TAXII client, fetching data from FS-ISAC's TAXII server based on a user-configured collection, parsing the intelligence, and ingesting it into ThreatQ. This feed adds additional features on top of ThreatQ's basic TAXII client functionality including, but not limited to, parsing object relationships out of STIX labels.
The integration provides the following feeds:
- FS-ISAC CDF - ingests intelligence from the FS-ISAC TAXII server.
- FS-ISAC Automated High
- FS-ISAC Automated Medium
- FS-ISAC Automated Low
- FS-ISAC Curated
- FS-ISAC Automated Vulnerabilities
The integration ingests the following system objects:
- Adversaries
- Attack Pattern
- Campaign
- Course Of Action
- Event
- Exploit Target
- Identity
- Identity Attributes
- Incident
- Indicators
- Intrusion Set
- Malware
- Report
- Report Attributes
- Signatures
- Tools
- TTP
- Vulnerabilities
- Vulnerability Attributes
Prerequisites
The following is required to use the integration:
- FS-ISAC TAXII Server Credentials
- ThreatQ's Egress IP Address whitelisted by FS-ISAC
Installation
Perform the following steps to install the integration:
The same steps can be used to upgrade the integration to a new version.
- Log into https://marketplace.threatq.com/.
- Locate and download the integration file.
- Navigate to the integrations management page on your ThreatQ instance.
- Click on the Add New Integration button.
- Upload the integration file using one of the following methods:
- Drag and drop the file into the dialog box
- Select Click to Browse to locate the integration file on your local machine
ThreatQ will inform you if the feed already exists on the platform and will require user confirmation before proceeding. ThreatQ will also inform you if the new version of the feed contains changes to the user configuration. The new user configurations will overwrite the existing ones for the feed and will require user confirmation before proceeding.
- The feed will be added to the integrations page. You will still need to configure and then enable the feed.
Configuration
ThreatQuotient does not issue API keys for third-party vendors. Contact the specific vendor to obtain API keys and other integration-related credentials.
To configure the integration:
- Navigate to your integrations management page in ThreatQ.
- Select the Commercial option from the Category dropdown (optional).
If you are installing the integration for the first time, it will be located under the Disabled tab.
- Click on the integration entry to open its details page.
- Enter the following parameters under the Configuration tab:
FS-ISAC CDF
Parameter Description TAXII Server Version Select the server version to poll data. Discovery Path URL Enter the path to the TAXII Server's Discovery Service. Options include: - 2.1 -
https://taxii.fsisac.com/ctixapi/ctix21/taxii2/(default) - 2.0 -
https://taxii.fsisac.com/ctixapi/ctix2/taxii/
Collection Name Enter the collection name to poll. Disable Proxies If enabled, the feed will not honor proxy settings set in ThreatQ. Username Enter your basic authentication username for FS-ISAC. Password Enter the password associated with the username above. Verify SSL Enable this parameter if the TAXII client should verify the provider's SSL certificate. Host CA Certificate Bundle Paste the certificate bundle in this field if you enabled the Verify SSL parameter. Ingest Stix Patterns as Signatures FS-ISAC reports IOCs using the Indicator STIX 2.1 object type. These objects represent one or more indicators using a STIX Indicator Pattern. By default, ThreatQ will parse and ingest these as both Signatures (STIX Indicator Pattern) and Indicators (atomic indicators). This field allows you to change that default behavior and exclude STIX Indicator Pattern Signatures from ingestion. Set indicator status to... Select the status to apply to indicators. 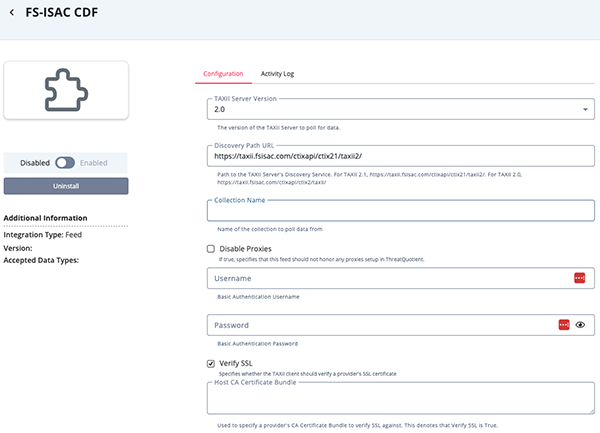
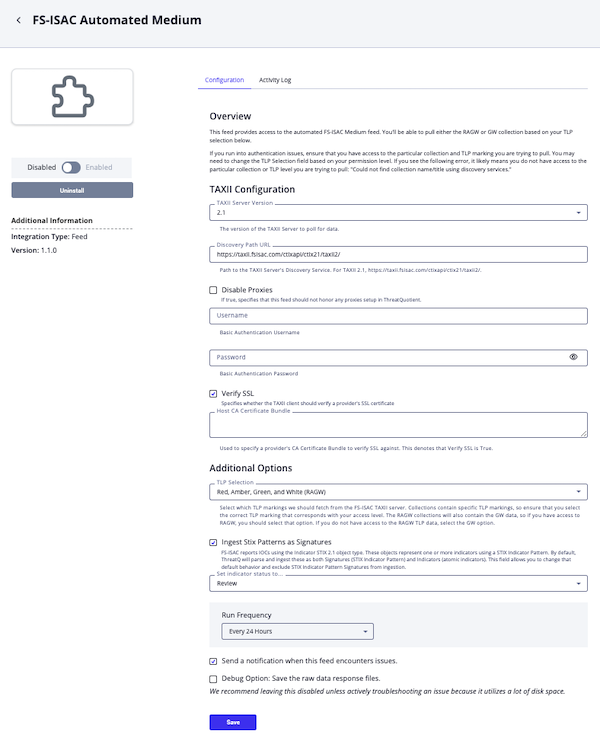
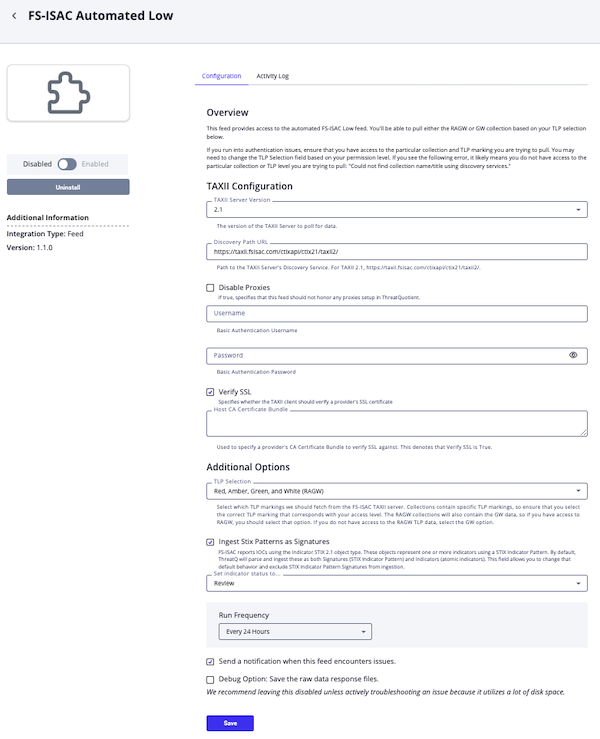
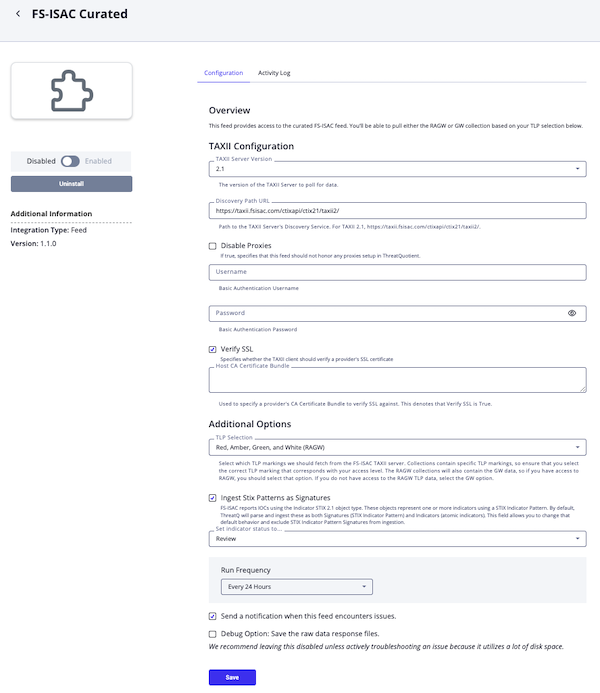
FS-ISAC Automated High, FS-ISAC Automated Medium, FS-ISAC Automated Low, and FS-ISAC Curated
Parameter Description TAXII Server Version Select the server version to poll data. Discovery Path URL Enter the path to the TAXII Server's Discovery Service. Options include: - 2.1 -
https://taxii.fsisac.com/ctixapi/ctix21/taxii2/(default) - 2.0 -
https://taxii.fsisac.com/ctixapi/ctix2/taxii/
Disable Proxies If enabled, the feed will not honor proxy settings set in ThreatQ. Username Enter your basic authentication username for FS-ISAC. Password Enter the password associated with the username above. Verify SSL Enable this parameter if the TAXII client should verify the provider's SSL certificate. Host CA Certificate Bundle Paste the certificate bundle in this field if you enabled the Verify SSL parameter. TLP Selection Select which TLP markings we should fetch from the FS-ISAC TAXII server. Collections contain specific TLP markings, so ensure that you select the correct TLP marking that corresponds with your access level. The RAGW collections will also contain the GW data, so if you have access to RAGW, you should select that option. If you do not have access to the RAGW TLP data, select the GW option.
- Red, Amber, Green, and White (RAGW) (default)
- Green and White (GW)
Ingest Stix Patterns as Signatures FS-ISAC reports IOCs using the Indicator STIX 2.1 object type. These objects represent one or more indicators using a STIX Indicator Pattern. By default, ThreatQ will parse and ingest these as both Signatures (STIX Indicator Pattern) and Indicators (atomic indicators). This field allows you to change that default behavior and exclude STIX Indicator Pattern Signatures from ingestion. Set indicator status to... Select the status to apply to indicators. 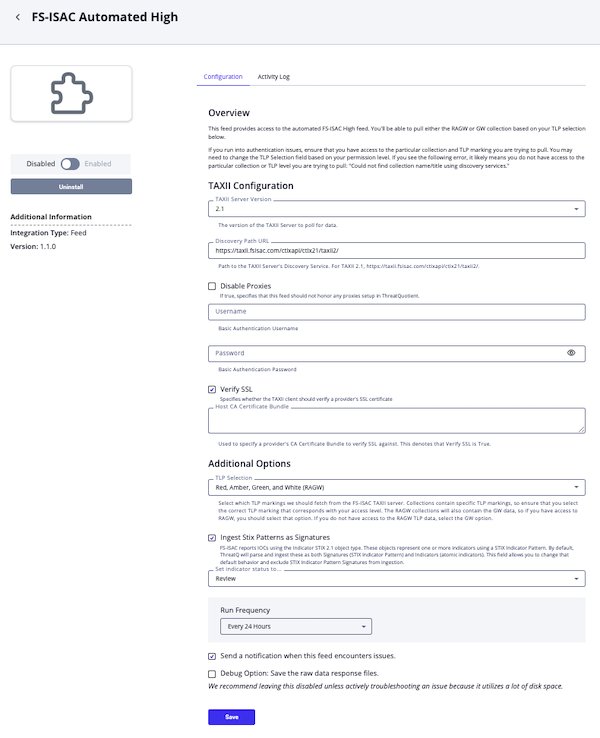
FS-ISAC Automated Vulnerabilities
Parameter Description TAXII Server Version Select the server version to poll data. Discovery Path URL Enter the path to the TAXII Server's Discovery Service. Options include: - 2.1 -
https://taxii.fsisac.com/ctixapi/ctix21/taxii2/(default) - 2.0 -
https://taxii.fsisac.com/ctixapi/ctix2/taxii/
Collection Name Enter the collection name to poll. Disable Proxies If enabled, the feed will not honor proxy settings set in ThreatQ. Username Enter your basic authentication username for FS-ISAC. Password Enter the password associated with the username above. Verify SSL Enable this parameter if the TAXII client should verify the provider's SSL certificate. Host CA Certificate Bundle Paste the certificate bundle in this field if you enabled the Verify SSL parameter. Ingest CVEs As... Select how you want CVE IDs to be ingested into ThreatQ. The Vulnerabilities that FS-ISAC reports may reference CVE IDs as references. We can parse and ingest these CVE IDs as either Indicators or Vulnerabilities. The benefit of ingesting them as Indicators is that they can be prioritized.
- Indicators (Type: CVE)
- Vulnerabilities (default)
Ingest Stix Patterns as Signatures FS-ISAC reports IOCs using the Indicator STIX 2.1 object type. These objects represent one or more indicators using a STIX Indicator Pattern. By default, ThreatQ will parse and ingest these as both Signatures (STIX Indicator Pattern) and Indicators (atomic indicators). This field allows you to change that default behavior and exclude STIX Indicator Pattern Signatures from ingestion. Set indicator status to... Select the status to apply to indicators. 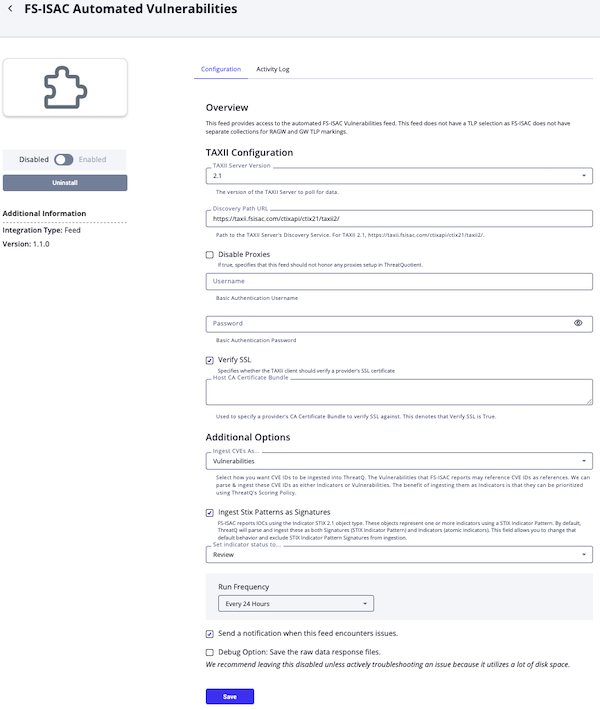
- 2.1 -
- Review any additional settings, make any changes if needed, and click on Save.
- Click on the toggle switch, located above the Additional Information section, to enable it.
ThreatQ Mapping
This integration ingests intelligence from the FS-ISAC TAXII server.
The majority of the parsing & mapping of the data is handled by the ThreatQ's generic STIX parser. See the STIX 2.0 Data Mapping topic for further details.
In addition, labels containing links to other entities will be converted into their corresponding object relationships. For instance:
malware:Lokibot-> A Malware object with the value,Lokibotthreat-actor:APT28-> An Adversary object with the value,APT28attack-pattern:T1059-> An Attack Pattern object with the value,T1001 - Data Obfuscation
Average Feed Run
Object counts and Feed runtime are supplied as generalities only - objects returned by a provider can differ based on credential configurations and Feed runtime may vary based on system resources and load.
| Metric | Result |
|---|---|
| Run Time | 1 minute |
| Indicators | 17 |
| Indicator Attributes | 31 |
| Adversaries | 4 |
| Malware | 10 |
Known Issues / Limitations
- Regarding TLP, the FS-ISAC API may return objects outside of the selected TLP range (gw or ragw)
- You will need to create multiple feeds in order to ingest from multiple collections. This requires that you install multiple instances of this integration. To do this, you will need to modify both the feed
nameandnamespacein the yaml file for each instance of the feed to avoid conflicts. These values must be unique.
To generate a Unique ID for Namespace:
- Open up a terminal window.
- Enter the following command:
uuidgen | tr "[A-Z]" "[a-z]"
Example Output:uuidgen | tr "[A-Z]" "[a-z]" b522dfcb-fe6c-4540-a8ed-76751d9bc8b0
- Copy and paste that unique ID to use as the new namespace.
- Enter the new feed name.
Example: FS-ISAC CDF > FS-ISAC CDF Collection 2
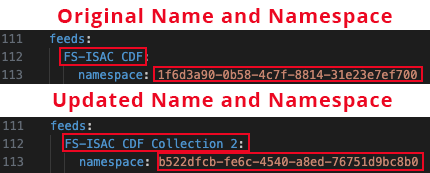
- Save the yaml file and proceed with the standard CDF install steps described in this guide.
Change Log
- Version 1.1.0
- Adds the ability to exclude STIX Indicator Pattern Signatures from ingestion
- Adds standardized FS-ISAC feeds based on known available collections.
- Version 1.0.2
- Resolved a
TypeErrorthat would occur with MITRE ATT&CK Patterns.
- Resolved a
- Version 1.0.1
- The integration will now appear under the Commercial category in ThreatQ Platform.
- The internal name for the TAXII Server Version configuration field has been updated.
- Version 1.0.0
- Initial release
PDF Guides
| Document | ThreatQ Version |
|---|---|
| FS-ISAC CDF Guide v1.1.0 | 5.29.0 or Greater |
| FS-ISAC CDF Guide v1.0.2 | 4.58 or Greater |
| FS-ISAC CDF Guide v1.0.1 | 4.58 or Greater |
| FS-ISAC CDF Guide v1.0.0 | 4.58 or Greater |